Why Integrating Cybersecurity Into IT Operations Is the Most Practical Path to Resilience
A few years ago, an urgent ticket came across the Third-Party Risk Review queue. A team had rolled out a new SaaS tool without a security review—again. Access logs were disorganized, user provisioning was manual, and the system had already been populated with sensitive data. When I checked in, the project lead told me, “We just needed to get it live. Security always slows things down.”

That moment clarified something I’d seen play out across roles and organizations: security wasn’t embedded – it was, to use a common industry phrase, “bolted on.” And because of that, it was often bypassed.
The truth is, most vulnerabilities don’t come from lazy teams or poor decisions. They stem from disconnection, or to put it another way, dis-communication: a deliberate choice, whether systemic or habitual, to exclude another party from the discussion. Security and IT operate on different timelines and face different incentives. That’s the issue.
IT is often incentivized to get solutions done quickly, cheaply, and well. Too often, the third criterion can be dropped if we can all convince ourselves and stakeholders that “we’ll come back to it to do it the right way later.” Ah, “later”. That mystical Shangri-la. That oasis in the desert of ServiceNow tickets and context switching.

InfoSec, however, is incentivized to protect the business, often by opposing the very things IT is rewarded for. If IT accelerates delivery by cutting corners, without proper risk acceptance processes, those risks remain unowned and unmanaged. But unlike IT, InfoSec doesn’t get credit for “almost” catching a vulnerability or “mostly” preventing a breach. The incentive is loss avoidance, not visible wins. That creates tension: IT is told to move fast; Security is held accountable when that speed causes a failure. It’s a structural mismatch—and without realignment, security will always be perceived as friction rather than a safeguard.
The solution isn’t more gates or more policies (though establishing these IS an essential foundation)—it’s integration. Real, operational alignment between cybersecurity and IT. That’s what actually builds resilience.
Rebuilding Trust Through Embedded Security
That IT team in the opening paragraph didn’t want to ignore security. They simply didn’t see how to include it. So we brought them into the process early the next time. We built a simple intake checklist—just a dozen questions—that IT owned but that included key security considerations. No gates, just awareness.
It changed everything.
Security became a shared responsibility, not an external audit. It was built in, not bolted on. Instead of a standoff, we had a conversation. And when risks were identified, they were addressed before launch, not after headlines.

Embedded security doesn’t mean giving up independence or oversight. It means recognizing that most risks are introduced—and can be prevented—by the same people managing systems every day. The most effective security leaders don’t just review controls. They help design them, hand in hand with IT.
From Compliance Theater to Operational Maturity
In another case, we were preparing for a compliance audit. The team was overwhelmed. Dozens of controls, unclear ownership, and a mountain of evidence to produce. The audit itself wasn’t the problem—it was that none of the practices had been truly operationalized.

We changed the approach. Instead of writing policies in isolation, we rewrote them with the people responsible for the systems. We asked, “What do you already do that mitigates this risk?” and aligned our documentation accordingly. Controls were mapped to real-world practices. The evidence? Already being produced.
Audits stopped being fire drills. Teams weren’t scrambling to prove something they’d never actually done. And when exceptions occurred, we had both context and accountability.
Good IT and Production security culture is not measured by passing audits. They will, but that isn’t the primary measure of success. Instead, they are the ones that build security into operations in such a way that audits become a natural byproduct of doing things right. Aligning your systems and processes to policy alone will help pass audits but this is the low bar. The policies are designed as a framework from which to build security directly into your process.
IT and Security Speak Different Languages—Until They Don’t
A client’s promising automation initiative was stalling out for weeks because IT and security couldn’t agree on the access model. The IT team needed speed and clarity. Security wanted granular controls and audit trails. Meetings went in circles.
So we tried something different. We built a joint working session. No slides, no roles—just a shared whiteboard. Within two hours, they’d mapped out an architecture that delivered both. It wasn’t perfect, but it was implemented and secure.
That collaboration only happened because we stopped treating security as a parallel function. Security must be part of IT’s design discussions, not just a reviewer of them. That’s how you build solutions that scale, secure by default.
The Right Control Is the One That Works

Some teams mistake restriction for security. They lock systems down so tightly that workarounds become inevitable. I’ve seen policies so rigid that teams resorted to personal email and shadow IT to get the job done. That’s not control—that’s collapse. This is how good security practices, applied without a proper understanding of business requirements, are what lead to breaches and major incidents. This may be hyperbolic, but overly complex password constraints set by well-meaning InfoSec and IT professionals may have kept the sticky note industry afloat for the past 30 years.
Too often, controls are designed to check a box or pass an audit—but that’s not the same as managing risk. A policy no one follows isn’t a control. And a control that isn’t tested under real-world pressure won’t hold when it matters. The most effective security measures aren’t the strictest—they’re the ones that blend effectiveness with practicality. They’re designed in partnership with the teams who use them, reinforced by culture, and adapted to stay relevant as the business and threats evolve. Real security isn’t about perfection—it’s about alignment between protection, behavior, and reality.
The Way Forward: Operationally Embedded Security
A resilient organization isn’t one with the most policies. It’s one where the people who build and run systems understand how to secure them, and are supported in doing so.
Here’s what that looks like in practice:
- Shared ownership of critical controls between IT and security
- Documentation that reflects real-world operations, not just framework language
- Automation that reduces friction where controls are most likely to be skipped
- Dialogue between teams that builds trust and supports informed decision-making
- Context-aware policies that support business velocity without sacrificing safety
When IT and security operate as one team, risk management becomes part of how things get done. Embedding security into operations follows three distinct stages
- Reactive
- Cooperative
- Embedded
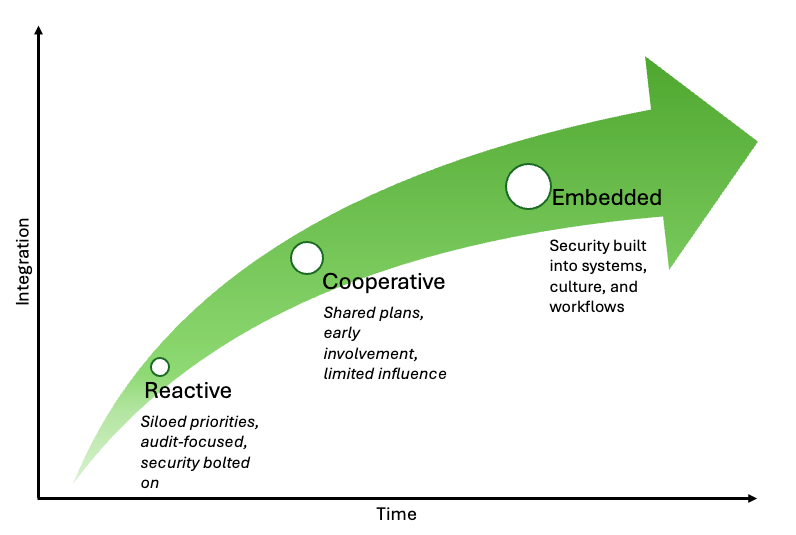
🔸 Reactive
Security is brought in too late. Most controls are theoretical or policy-based, and risk is uncovered through incidents or audit scramble.
First step: Establish a shared intake process to ensure IT and Security are engaged from project inception.
🔸 Cooperative
Security is consulted earlier, and policies reflect reality, but enforcement is inconsistent, and ownership is unclear.
First move: Start co-owning simple controls and tie them to delivery metrics.
🔸 Embedded
Security becomes part of how IT works: from system design to deployment. Risk decisions are made in real time and supported by both teams.
First move: Build automation and monitoring into your pipelines, not around them.
Get started…
Resilience isn’t built in checklists or dashboards. It’s built in relationships—between teams, between systems, and between decisions made under pressure.
Download the Embedded Security Maturity Playbook for deeper guidance, including templates, play-by-play examples, and metrics. Subscribe to our blog for future articles covering case studies, automation frameworks, and how to build executive-aligned security programs.
Related Reading
Explore these valuable resources from trusted sources in security and DevSecOps:
- AWS OT/IT Convergence Security Maturity Model – Practical maturity model for converging IT/OT security https://aws.amazon.com/blogs/security/ot-it-convergence-security-maturity-model/
- The DevSecOps Capability Maturity Model (SEI) – Roadmap for weaving security into DevOps SEI
- Security Culture Maturity Model (Keepnet Labs) – Framework to assess and improve security behaviors in daily operations https://keepnetlabs.com/blog/what-is-the-security-culture-maturity-model

